Seoul, Hong Kong, New Delhi, Beijing, London, Buenos Aires, San Diego – January 29, 2021
Apple and Huawei implement embedded hardware security through a secure element (eSE/inSE).
Samsung uses a physically unclonable function (PUF).
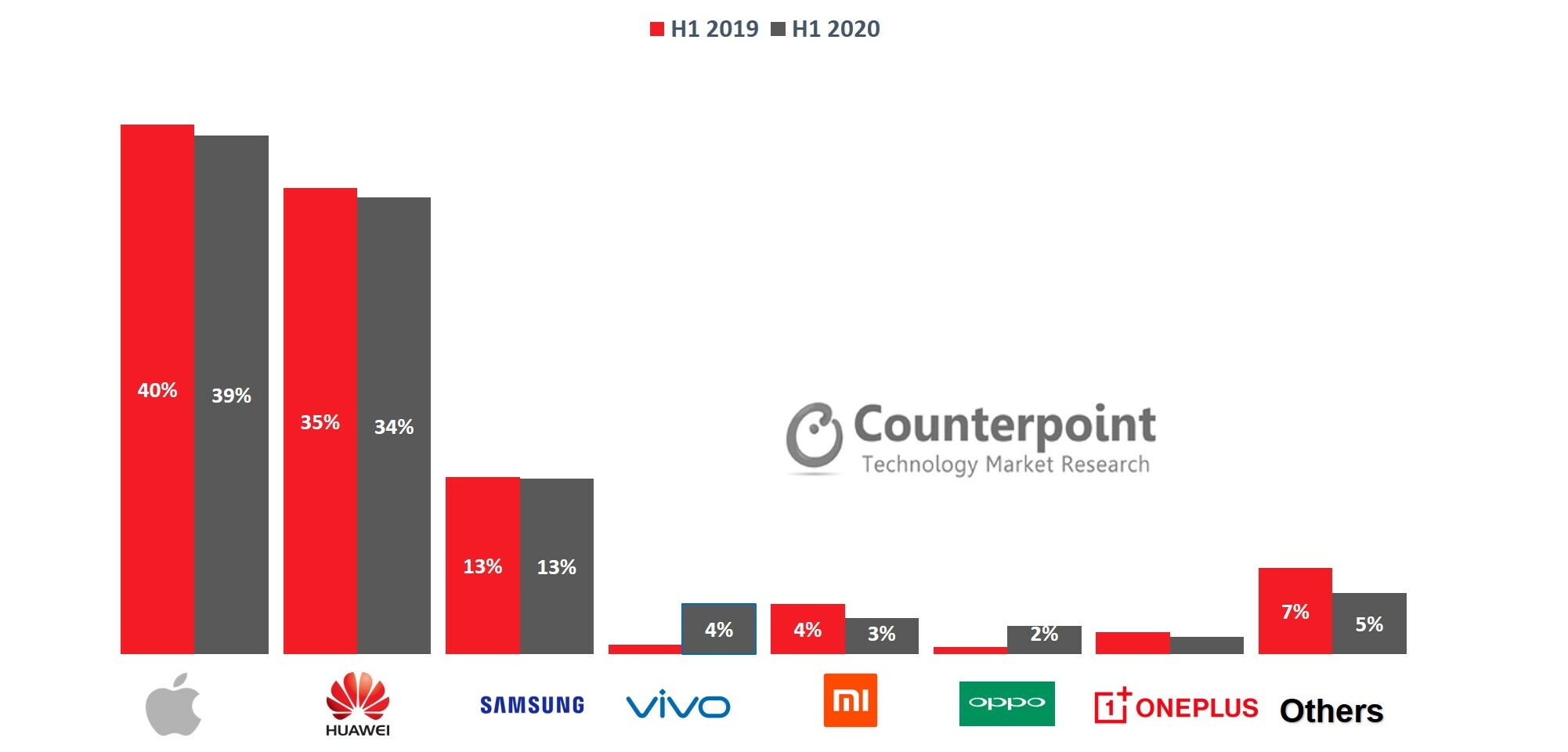
Hardware security was embedded in 35% of the smartphones sold globally in H1 2020, according to the latest research from Counterpoint’s Component Practice. This share is expected to reach 38% in 2021. Apple led the secure chipset market in H1 2020 with 39% share.
Commenting on smartphone security, Research Analyst Parv Sharma said, “Smartphones have become vulnerable to attacks. We use them for banking, financial transactions, biometrics, user data and even as digital keys for smart homes and automobiles. Therefore, the need for hardware security in smartphones is stronger than ever.”
Sharma added, “Hardware security is being adopted not only in the premium segment smartphones but has trickled down to the mid-segment as well. The sales of secure smartphones declined 6% in H1 2020 compared to H1 2019. The decline is due to the outbreak of COVID-19 pandemic, which led to reduced overall smartphone sales in H1 2020.”
Exhibit 1: Global Sales of Smartphones with Embedded Hardware Security: Market Share in H1 2020 vs H1 2019
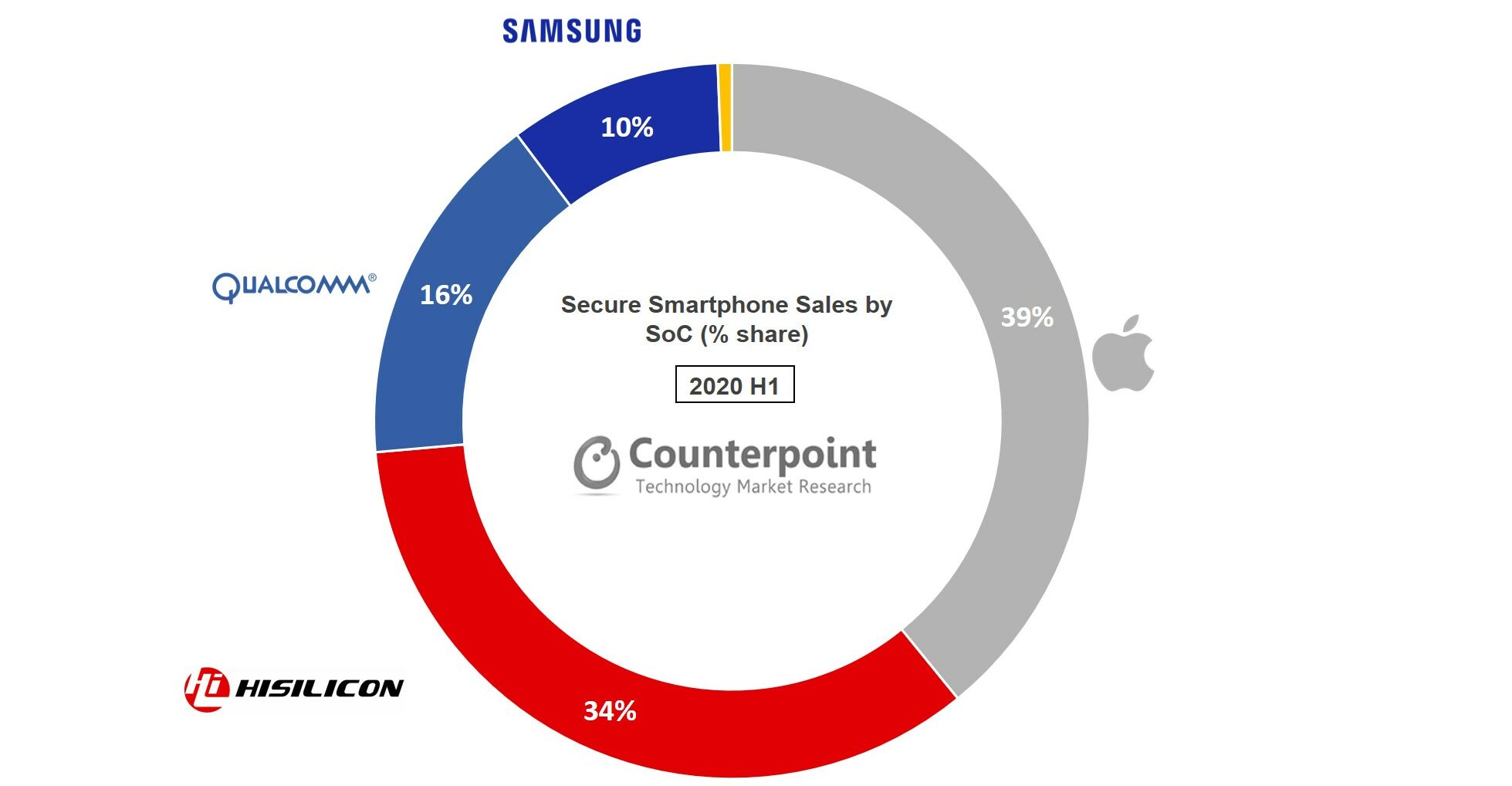
Commenting on the competitive landscape in the secure chipset market, Research Vice President Neil Shah said, “Hardware-backed security (strong box) means that keys are stored in the secure element, which is a separate microchip. , a trusted execution environment (TEE) is a secure area of the main processor which runs its OS and communicates with the main OS via a restricted interface. The strong box approach is more secure. Chipset OEMs have embedded eSE their SoC. Apple’s portfolio for 2020 has an embedded secure element in the A Series chipsets. Apple led the secure chipset market with 39% share in H1 2020.”
Shah added, “Huawei has also implemented an integrated secure element (inSE) in its SoCs. But its share will decline due to US restrictions. Qualcomm has adopted a secure element as a secure processing unit (SPU) in the Snapdragon 800 Series. It has also trickled down to the Snapdragon 700 Series in the mid-end segment. Samsung implements a physically unclonable function (PUF) which serves as a unique identifier. Samsung has also used a Quantum Random Number Generator (QRNG) in the Galaxy A Quantum to make the device more secure.”
Exhibit 2: Global Sales of Smartphones with Embedded Hardware Security by SoC Vendor, H1 2020 (Excluding TPM)
 The comprehensive and in-depth report on “Global Secure Smartphone Sales by Model Tracker” is a part of our Security service. The report is available for download here.
The comprehensive and in-depth report on “Global Secure Smartphone Sales by Model Tracker” is a part of our Security service. The report is available for download here.
Background
Counterpoint Technology Market Research is a global research firm specializing in products in the TMT (technology, media and telecom) industry. It services major technology and financial firms with a mix of monthly reports, customized projects and detailed analyses of the mobile and technology markets. Its key analysts are experts in the high-tech industry with an average tenure of 15 years.
Analyst Contacts:
Counterpoint Research
press(at)counterpointresearch.com


